Please email me at:
Or use the form below.
[contact-form 1 “Contact form 1”]
The no-pants guide to spending, saving, and thriving in the real world.

No one likes to think about the possibility of dying too young. But knowing that potential exists, you take the smart step of protecting those you love by carrying term life insurance. But what about preventing the worst? Did you know your iPhone or Android device can call for help or record vital information if you ever find yourself in a life-threatening situation? Here are five personal safety apps that could save your life.
1) myGuardianAngel
Once this app allows you to reach all of your emergency contacts with the push of one button. You enter the contact information for anyone you would want to get in touch with if you were in any sort of emergency as soon as you download it. If you are in an emergency, the app will call your contacts, send them an e-mail with your GPS location and immediately begin recording audio and video from your phone.
2) StaySafe
This app is good for anyone who works or travels alone. You can schedule the app to automatically notify friends or family after a certain period of time when your phone is inactive. For example, you can estimate how long you expect to drive from one location to another on your own and then the phone will contact someone automatically if you are out of contact longer than expected. That way your friends will know to send help because something is wrong, even if you aren’t in a position to contact them yourself. StaySafe sends your contacts a detailed GPS location for you so that they can easily find you and bring help.
3) RESCUE
This full-service app can help you on the scene as well as notify your emergency contacts for you. If you are in trouble, you can trigger the app to sound a loud alarm that might frighten off anyone who might be planning to do you harm. The alarm can also help someone find you if you are lost or unable to move from your current location. When the alarm is triggered, the app will also send immediate notifications to your emergency contact list so that they can begin to send help right away. Emergency services such as the police and fire department can also be set for notification through the RESCUE app.
4) Night Recorder
This is a good app to have when you need to make a quick recording of your surroundings for any reason. The app can be set to begin recording at a touch. If you are stranded, you could create a recording by speaking about the landmarks you can see and explaining how you got to your current location. The recorder can then send an email of your recording to anyone on your contact list.
5) iWitness
With this app, you can instantly make video or audio recordings of your situation so that there is a permanent first-hand record of everything that happens. It is a handy tool for anyone who has been in a car accident or involved in a medical emergency because you can go back and look at the video to see exactly what happened if there is any question about it later. The app will also contact emergency services or your personal emergency contacts if you are in trouble. The built-in GPS locator will transmit your exact location so that people can find you quickly and easily.
Post by Term Life Insurance News
In this installment of the Make Extra Money series, I’m going to show you how to set up a WordPress site. I’m going to show you exactly what settings, plugins, and themes I use. I’m not going to get into writing posts today. That will be next time.
I use WordPress because it makes it easy to develop good-looking sites quickly. You don’t have to know html or any programming. I will be walking through the exact process using Hostgator, but most hosting plans use CPanel, so the instructions will be close. If not, just follow WordPress’s 5 minute installation guide.
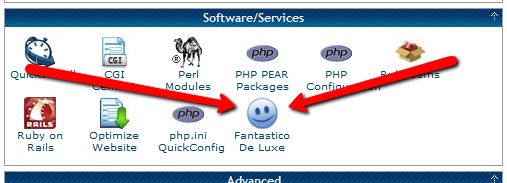
Assuming you can follow along with me, log in to your hosting account and find the section of your control panel labeled “Software/Service”. Click “Fantastico De Luxe”.
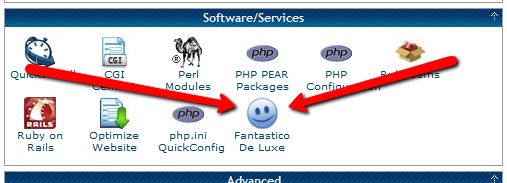
On the Fantastico screen, click WordPress, then “New Installation”.
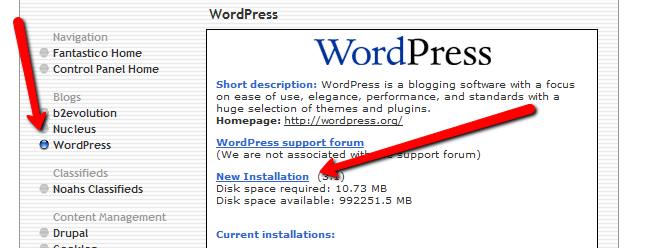
On the next screen, select your domain name, then enter all of the details: admin username, password, site name, and site description. If you’ll remember, I bought the domain http://www.masterweddingplanning.net. I chose the site name of “Master Wedding Planning” and a description of “Everything You Need to Know to Plan Your Wedding”.
Click “install”, then “finish installation”. The final screen will contain a link to the admin page, in this case, masterweddingplanning.net/wp-admin. Go there and log in.
After you log in, if there is a message at the top of the screen telling you to update, do so. Keeping your site updated is the best way to avoid getting hacked. Click “Please update now” then “Update automatically”. Don’t worry about backing up, yet. We haven’t done anything worth saving.
Next, click “Settings” on the left. Under General Settings, put the www in the WordPress and site URLs. Click save, then log back in.
Click Posts, then Categories. Under “Add New Category”, create one called “Misc” and click save.
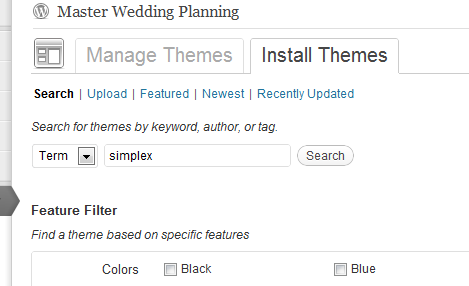
Click Appearance. This brings you to the themes page. Click “Install Themes” and search for one you like. I normally use Headway, but before I bought that, I used SimpleX almost exclusively. Your goal is to have a simple theme that’s easy to maintain and easy to read. Bells and whistles are a distraction.
Click “Install”, “Install now”, and “Activate”. You now have a very basic WordPress site.
A plugin is an independent piece of software to make independent bits of WordPress magic happen. To install the perfect set of plugins, click Plugins on the left. Delete “Hello Dolly”, then click “Add new”.
In the search box, enter “plugin central” and click “Search plugins”. Plugin Central should be the first plugin in the list, so click “install”, then “ok”, then “activate plugin”. Congratulations, you’ve just installed your first plugin.
Now, on the left, you’ll see “Plugin Central” under Plugins. Click it. In the Easy Plugin Installation box, copy and paste the following:
All in One SEO Pack Contact Form 7 WordPress Database Backup SEO SearchTerms Tagging 2 WP Super Cache Conditional CAPTCHA for WordPress date exclusion seo WP Policies Pretty Link Lite google xml sitemaps Jetpack by WordPress.com
Click “install”.
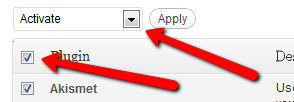
On the left, click “Installed Plugins”. On the next screen, click the box next to “Plugins”, then select “Activate” from the dropdown and click apply.
Still under Plugins, click “Akismet Configuration”. Enter your API key and hit “update options”. You probably don’t have one, so click “get your key”.
The only tool I worry about is the backup. It’s super-easy to set up. Click “Tools”, then “Backup”. 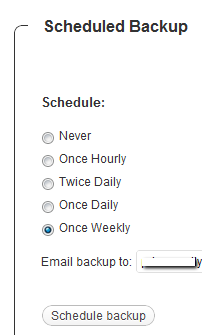
Scroll down to “Schedule Backups”, select weekly, make sure it’s set to a good email address and click “Schedule Backup”. I only save weekly because we won’t be adding daily content. Weekly is safe enough, without filling up your email inbox.
There are a lot of settings we’re going to set. This is going to make the site more usable and help the search engines find your site. We’re going to go right down the list. If you see a section that I don’t mention, it’s because the defaults are good enough.
Set the Default Post Category to “Misc”.
Visit this page and copy the entire list into “Update Service” box. This will make the site ping a few dozen services every time you publish a post. It’s a fast way to get each post indexed by Google.
Click “Save Changes”.
Uncheck everything under “Email me whenever…” and hit save. This lets people submit comments, without actually posting the comments or emailing me when they do so. Every once in a while, I go manually approve the comments, but I don’t make it a priority.
Select “Custom structure” and enter this: /%postname%/
Click save.
Set the status to “Enabled”, then fill out the site title and description. Keep the description to about 160 characters. This is what builds the blurb that shows up by the link when you site shows up in Google’s results.
Check the boxes for “Use categories for META keywords” and “Use noindex for tag archives”.
Click “Update Options”.
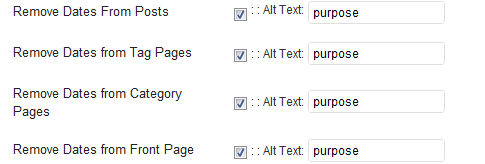
Check the boxes to remove each of the dates and set the alt text to “purpose” or something. This will suppress the date so your posts won’t look obsolete.
This plugin reinforces the searches that bring people to your site. It’s kind of neat. Skip the registration, accept the defaults and hit save.
Scroll to the bottom and click import. We’ll come back to this.
Select “Caching On” and hit save.
Across the top of the screen should be a giant banner telling you to connect to WordPress.com and set up Jetpack. You’ll need an account on WordPress.com, so go there and set one up. After authorizing the site, you’ll be brought back to the Jetpack configuration screen. Click “Configure” under “WordPress.com Stats”. Take the defaults and hit save.
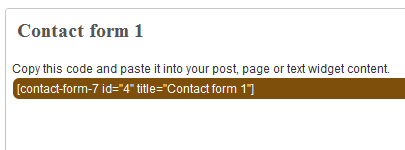
On the contact configuration page, copy the code in the top section. You’ll need this in a moment.
Now, we going to create a couple of static pages. On the left, click “Pages”, then “Add new”.
Name the first page “Contact” and put the contact form code in the body of the page. Hit publish.
Under Appearance, click “Menu”. Enter a menu name and hit save.
Then, under “Pages”, click the box next to “Contact”, “Disclaimer”, and any other policies you’d like to display. Hit save.
Also under Appearance, click “Widgets”. This is where you’ll select what will display in the sidebar. All you have to do is drag the boxes you want from the middle of the page to the widget bar on the right. I recommend Text, Search, Recent Posts, Popular Search Terms and Tag Cloud. In the text box, just put some placeholder text in it, like “Product will go here”. We’ll address this next time.
We’re not going to worry about getting posts in place, yet. That will be the next installment. However, the steps in the next installment could take 2 weeks to implement, and we want Google to start paying attention now. To make that happen, we need to get a little bit of content in place. This won’t be permanent content. It’s only there so Google has something to see when it comes crawling.
To get this temporary, yet legal content, I use eZineArticles. Just go search for something in your niche that doesn’t look too spammy.
Then, click “Posts”, then delete the “Hello World” post. Click “Add new”. Copy the eZine article, being sure to include the author box at the bottom, and hit publish.
To see your changes, you may have to go to Settings, then WP Cache and delete the cache so your site will refresh.
Congratulations! You now have a niche blog with content. It’s not ready to make you any money, yet, but it is ready for Google to start paying attention. In the next installment, I’ll show you how I get real unique content and set it up so Google keeps coming back to show me the love.
There are two options to choose from.
As some of you have noticed, the link to subscribe by email has changed. While you do still have the option to subscribe to the rss feed through Feedburner, I’m no longer providing the link or recommending it. What I have in its place is an actual email list.
Yes, you can now subscribe to Live Real, Now by email, without having to go through Feedburner. That means you can get all of the updates in your email, for free! This is magic. This magic gives me another option to offer contests and free stuff.
There are two lists to choose from.
Your email will never be shared, with anyone, for any reason whatsoever. Ever. I hate spammers with a passion fueled by the fiery pits of hell to which spammers should be cast. I won’t be that guy.
Please, take this chance to subscribe to the magic.
Skip to the bottom if you’re familiar with PRISM and don’t want to hear any political talk and rampant violations of our Constitutional rights, but still want to protect your privacy.
For those of you who haven’t been paying attention, the PRISM program is an NSA program to monitor electronic activity.
Lots of electronic activity.
The companies identified to be working with the NSA in this grand overreach include AOL, Apple, Facebook, Google, Microsoft, PalTalk, Skype, Yahoo! and YouTube. For most people, that is the definition of “the internet”. If you’re doing it online, the NSA is–or could be, at their leisure–watching.
This isn’t a crazy conspiracy theory. This is happening, and the government has admitted it. In fact, when this broke, the executive branch’s response was along the lines of, “Don’t worry, we’ll find the guy who leaked this information.”
On top of that, the government has been demanding phone records from at least Verizon on a daily basis.
In addition, the Justice Department was just busted wiretapping Associated Press phones.
Seriously, if you put this in fiction, nobody would buy it, because it’s ridiculous in the land of the free.
As far as the people who say I’ve got nothing to worry about if I’m not doing anything wrong: shut up. You can speak again when you give me your email passwords, bank records, and let me install a toilet cam in your house. What are you trying to hide?
Seriously, there is such a mess of non-legislative administrative regulations that are considered felonies that the best estimate is that most people commit three felonies a day, without realizing it.
When we live in a system with so many rules that have never been voted on and our legal system refuses to consider legitimate ignorance of the law to be a defense and we have a collection of secret laws that are a felony to disclose or violate, government spying gets far more dangerous.
The Foreign Intelligence Surveillance Act of 1978(FISA) is the law the NSA is using to justify all of these data requests. The law, that we all must obey, is being overseen by a small subcommittee in Congress, and the FISA courts are just a small subset of the judges. The judges are signing warrants allowing the wiretaps and massive surveillance, but that is clearly unconstitutional and, hence, illegal.
The text of the Fourth Amendment to the Constitution, the supreme law of the United States is: “The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no Warrants shall issue, but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.”
Any warrant that cannot name a place to be searched is illegal.
Any warrant that cannot describe the person to be monitored is illegal.
Any warrant that is not backed by probable cause is illegal.
Tell me how “I want to watch what everyone is saying on Facebook and seize all of the data” meets any of those criteria.
Bueller?
Wiretapping the AP is a serious violation of the First Amendment, too. “Congress shall make no law respecting an establishment of religion, or prohibiting the free exercise thereof; or abridging the freedom of speech, or of the press; or the right of the people peaceably to assemble, and to petition the Government for a redress of grievances.”
“Congress shall make no law…abridging the freedom of speech, or of the press..and to petition the Government for a redress of grievances.”
Monitoring the press in case somebody breaks a story the government doesn’t want broken is crap.
How can we petition the government for redress of grievances that they call a felony if the company discloses the violation to us? It’s self-serving circular crap.
When you throw the IRS harassing charities working for the “wrong” politics, you start to pine for the good old days of Nixon-level fair play and integrity.
To be fair, FISA got nasty with the Patriot Act, which was an abomination enacted by a different political party. Hey, Washington, next time try to remember that your laws will someday be administered by your political enemies, k? (NSA: I trust you’ll pass the message for me?)
There are four main pieces to discuss, based on the scandalous Constitutional violations reported recently.
1. Social media monitoring. There’s nothing to this. If you post things on Facebook, the government sees it and knows it’s you. Don’t post anything you don’t want broadcast to the police, your grandmother, and your priest.
2. Internet browsing. There is very little that is secure on the internet. The government can subpoena your ISP and get any records they keep. Unless you go anonymous and encrypted. Welcome to TOR. The Onion Router is a system that encrypts your internet traffic and bounces it all over the world. Once you enter TOR, nothing you do can be tracked, until your internet request leave the TOR system. The system is not centrally owned or controlled, so nobody in the system can track what you are doing.
For example, if I use the TOR browser to search Wikipedia, a snoopy NSA goon could tell I’m using it, and they could tell there was a request from the TOR system to Wikipedia, but they can’t tie one request to the other. If I’m dumb and log into Facebook, I lose that anonymous shield.
That’s solid protection from anyone watching your internet traffic.
How do you use it?
Easy. Just install the Tor Bundle. When you want the NSA to stop snooping over your shoulder because you want to do a search on erectile dysfunction, you launch TOR and the TOR browser and search without having to share your embarrassing secrets.
3. Email. Email is easily the least secure means you can communicate. When you send an email, that message is in plain text, and it bounces from server to server until it reaches the recipient. Any of the involved servers can keep a log of the traffic and read your email.
Never, ever, ever, ever put anything incriminating or important in an email. Don’t send credit card numbers, your social security number, or the address of your meth lab.
But what if you want to have a dirty conversation with your spouse without letting the sick voyeurs at the NSA listen to you ask your wife what she’s wearing and how would she like it torn off?
Use PGP. OpenPGP is a free software encryption program that is basically impossible to decrypt. It’s known as public-key encryption, which means that anybody can encrypt a message to you that only you can read.
It’s like magic.
To use PGP, the easy way(for Windows users) is to get Gpg4win. Install that, then open Kleopatra. This will let you generate your encryption key. You do that by:
You now have a set of PGP keys. To get your public key that others can use to send you messages, right-click your certificate and select “Export certificates”. Pick a path to save the certificate, then do so. You can open this file with notepad to get your public key, or you can email the file out. There is no need to worry about security with this file.
You will end up with something that looks like my public key here:
—–BEGIN PGP PUBLIC KEY BLOCK—–
Version: GnuPG v2.0.20 (MingW32)mQENBFGyPPkBCAC8zc5B7srG/ZyRMpokP3KyIMd9GA4n94wT89sP/yWFylbTKXDM
S2vC0yXh4zDJshJ1odj+spJGeYaXHCJM21buzKYf0gZsUGIbkVZWRy8ch16+umFl
DuTMaCN5Yue6ehGsjH8N+4q7pmXSlyRXRXzG0A4d9de4SQnfO65e1CMaQhFMpJu0
mXK8KFLqJ560efzlTTZvN3o5RfxYhtB3ODoDfkGeBLIxGVYn1kYbowTcvwymATOb
iSHwNfH+vY+kuTnrG9ilLyprDKwAF+ErD87WP0pLKVIQvoMV69VHEoRhHqK45iJG
j0ZhtTA4emnGZtCNsdfPLUdws1k9SNeIpd9pABEBAAG0H0phc29uIDxqYXNvbkB3
YWxiZXJnb25saW5lLmNvbT6JATkEEwECACMFAlGyPPkCGw8HCwkIBwMCAQYVCAIJ
CgsEFgIDAQIeAQIXgAAKCRDRFT/09vSoj10ECACVE/ngHyzX1lnMlucW4Rx8b8ii
KK8v/AmVkrJZgI3umuJn906sGGA8fNjxUGYH5fX6R7Diud4SEnZWADSq5pAImOv+
qZnPdpJKjMaY6qr+trr0DGsCoen+TxzM7rClBz3TTURI5SbySojHvQoEiCHHPBw1
yY3+leoUzLmso98ocA2lY4Iuvr7/fAzuQEFhBdxxLtS7mDWdmUca+A6GsrCr4LZ7
fpovRCNv07BoAa5ql+GrPOcsIcLwSoEtkhjCo4vPDeveqsnLT0W7N9YBPiGMpHPm
0oFxniC6/eWtI+3C8QFYO3X+CC5yTYpqJJ0BJWhXjiqYmr290d3AN+hYck3T
=fHba
—–END PGP PUBLIC KEY BLOCK—–
To get your private key, that you can use with any number of plugins for your email client, right-click on your certificate and select “Export secret keys.”
You can either use PGP as a plugin for your email client, or you can use Kleopatra’s feature “Sign/encrypt files”. To do that, write your message in a file, then select the feature inside Kleopatra. You’ll end up with an encrypted file you can attach to your email that snoopy government man can’t read.
4. Phone calls. This would appear to be harder, since your phone is largely out of your control. There’s nothing practical you do about a landline, except to avoid saying anything sensitive. On your cell phone, you have options, assuming you use a smartphone.
For Android users, it’s free an easy. Install Redphone. If you place a call with Redphone, it checks to see if the caller also uses Redphone. If he does, it places an encrypted call over your data plan to the other phone. Nobody can listen in to an encrypted call. The same company also makes a program for texting.
For iPhone users, you’re stuck with Silent Circle for $10/month, which may be a better option, since there is support for more devices, including Android. It was designed by the guy who designed PGP and handles texting and email, too.
There you are, the whats, whys, and hows of modern, hassle-light, private communications. Doing what we can to foil bad government programs is our patriotic duty.